PIA or DPIA: What’s the Difference?

Cyberspace contains petabytes of private information. Whether furnished by the users on a formal request from the online service providers or exposed voluntarily in social media networks, personal information is always an attractive target for cybercriminals.
Definition: What is a privacy impact assessment and data protection impact assessment
- Privacy Impact Assessment (PIA) is all about analyzing how an entity collects, uses, shares, and maintains personally identifiable information, related to existing risks.
- Data Protection Impact Assessment (DPIA) is all about identifying and minimizing risks associated with the processing of personal data.
How are PIA and DPIA different?
The Privacy Impact Assessment (PIA) is a process used to protect privacy by design when an organization starts or acquires a new business, implements a new process, or launches a new product. The Data Protection Impact Assessment (DPIA) is an ongoing process, regularly applied to personal data processing, identifying, and mitigating risks. The DPIA is a part of the European Union (EU) General Data Protection Regulation (GDPR) compliance activities.
Data Protection Kit will enable quick and efficient management of the data protection systems with preinstalled PIA reporting options and much more.
PIA and DPIA Fundamentals
The basic principles of PIA and DPIA are similar. It is an iterative cycle of four sequential stages:
- Defining the context of personal data processing;
- Establishing controls to ensure compliance with the fundamental principles;
- Assessing associated privacy risks;
- Validating the attained data protection level.
Key items you need to define during each stage of a PIA or DPIA:
- The parties (data controllers, processors, and subjects);
- The data nature and scope;
- The purposes of data processing;
- The compliance requirements under GDPR and/or other legislation.
When is a DPIA Required under GDPR?
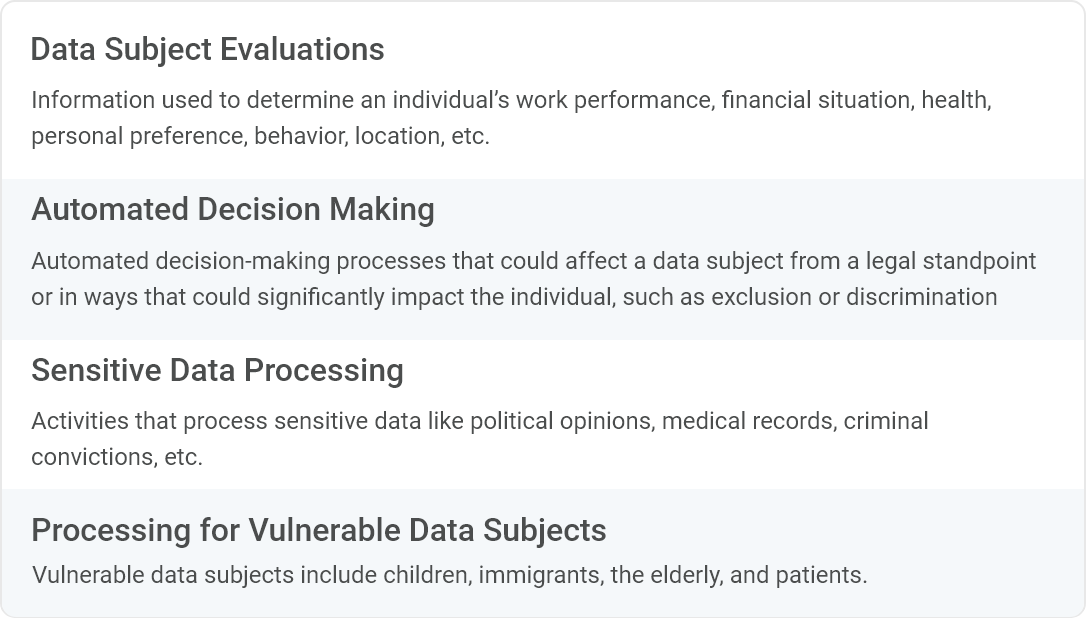
The EU GDPR requires companies to perform a DPIA before specific data processing types to ensure they can mitigate risks. Article 29 of the EU Working Party Guidelines for GDPR lists activities eligible to DPIA.
Some of the data-related events that may trigger a DPIA:
- Likelihood of high risks to data subjects’ rights and freedoms
- Introduction of new data processing processes, systems, or technologies.
- Implementation of extensive systematic profiling with essential effects.
- Large-scale processing of criminal offense info or special category data Systematic monitoring of publicly accessible places on a large scale.
Some EU member states (and the UK) create national ‘Blacklists’ and ‘Whitelists’ to guide which processes do and do not require DPIA. Compliance Aspekte will help you to identify relevant requirements in the countries you operate in.
When is PIA required?
The PIA is a comprehensive analysis of how PII (personally identifiable information) is collected, stored, shared, managed, and protected. Companies must start PIAs early in project development or design and consider them throughout the lifecycle with the privacy impact assessment template.
Data processing activities that may lead to a PIA
- Conversion of paper-based records to electronic systems.
- Changes of anonymous information to non-anonymous.
- New implementation of existing IT systems (i.e., application of new technologies).
- Essential merging of databases holding sensitive information.
- New public access of user-authenticating technology (e.g., password, digital certificate, biometric).
- Information is obtained from commercial or public sources.
- New uses of information between data processing agencies (e.g., cross-cutting E-Government initiatives).
- Changes of a business process that results in new uses or disclosures of information
- Addition of new information to a collection.
PIA solutions
How can you simplify the process of managing PIA and DPIA along with other standards?
Standards Compliance Manager is a cloud-based solution designed explicitly for comprehensive compliance and multiple standard management. It is easily tailored to your business needs due to extensive customization capabilities and comprises privacy impact assessment best practices.
Compliance Aspekte also provides an initial Discovery to determine how best to apply Privacy and Data Protection Impact Assessments in your organization. The solution will enable you to engage fresh eyes on the topic of compliance, about PIA or DPIA considerations, and crucially, quickly identify areas of vulnerability and quick-win solutions.
Try Compliance Aspekte For Free
Book a 1-2-1 Live Demo and Obtain a 3-months Non-binding Trial
Effective and easy-to-use IT security management system based on the latest standards and regulations — from planning and establishing the security concept to certification.
