Everything You Need to Know about RoPA for Your GDPR Compliance
Introduction of General Data Protection Regulation (GDPR) in May 2018 has turned a lot of things for companies upside down. One of the challenges which came together with this tough set of data protection rules was the Record of Processing Activities (RoPA). If the company fails to keep it, the fines can reach up to 10 million euros or 2% of its annual turnover.
In our article, we will find out what is RoPA, what info it has to contain, and who is responsible for its maintenance. Moreover, we will outline the best way to implement this GDPR requirement on practice.
What is a Record of Processing Activities (RoPA)?
Article 30 of the GDPR states that the controllers and processors must create and maintain the records of processing activities that take place within the organization. This document should include the list of each processing activity of the personal data maintained in a written or electronic format. So, whenever the company collects, uses, stores,or transfers any kind of such data, it needs to create or constantly update such records. Moreover, businesses should meet the data protection principles.
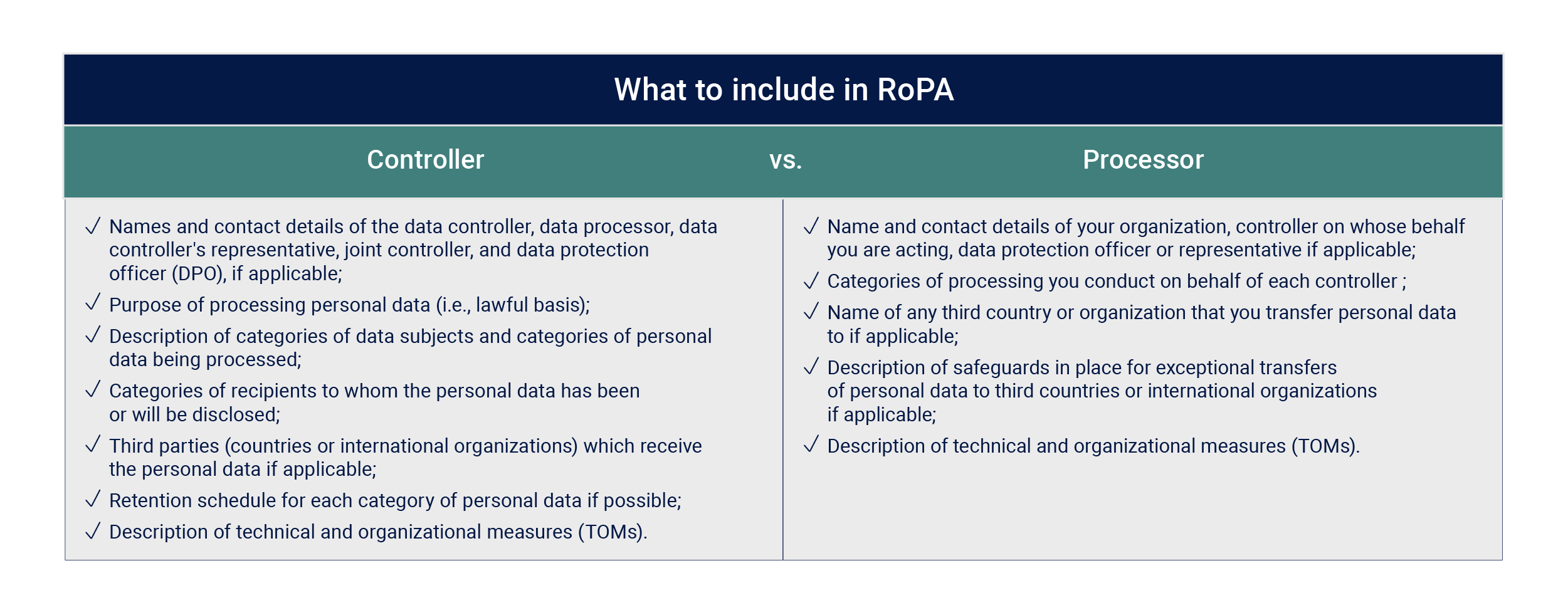
Information You Should Include in RoPA
The list of information that RoPA should include differs for controllers and processors. The controllers decide why and how the data is collected and processed, while the data processors’ main responsibility is to execute its processing on behalf of a controller.
Who needs to document the processing activities?
Generally, only the organizations with 250 or more employees must maintain a RoPA. However, this GDPR compliance requirement may also apply to smaller companies if their processing activity:
- is likely to result in a risk to the rights of affected people (e.g., comprehensive monitoring, use of new technologies)
- is not occasional (e.g. such daily activities as customer management or salary management)
- includes special categories of data as referred to in Article 9 (1) (e.g., health data, biometric data) or personal data relating to criminal convictions and offenses referred to in Article 10.
Therefore, it is also obligatory for a lot of small and medium-size companies to maintain their records.
How to create and maintain a RoPA
The main steps for creating and maintaining RoPA are outlined below:
- Audit of all available personal data – a good idea when starting with a RoPA is to do some audit of information to clarify what personal data the company holds, where, and how it processes it.
- Identification of the role – for each processing activity, it is necessary to identify whether you are a controller or a processor. For US-based companies doing business in EU the GDPR requirements will be the following: you have to appoint an EU-resident and mandate him/her to act on your behalf with regard to the obligations under GDPR compliance.
- Categorization of data – a very important step before documenting your activities is breaking down the data that you have on data subjects into categories.
- Documentation of activities – you should keep records in written and electronic form. It is also important to do it in a structured and meaningful way. Moreover, if the records must be kept, they should be stored in a centralized way.
- Constant updating – you should keep your register under regular review. Whenever your organization starts new processing activities or changes the purpose of its current ones, the register must be updated.
Managing RoPA with Compliance Aspekte
The manual creation of RoPA under GDPR compliance requirements or using tools like Excel may be very difficult and time-consuming. Better to consider a modern GRC solution like Compliance Aspekte which can solve your primary challenges. It provides the necessary functionality for creating and maintaining RoPA efficiently. Compliance Aspekte offers advanced customization possibilities, so you will be able to generate RoPA lists tailored to your specific business needs.
Try Compliance Aspekte For Free
Book a 1-2-1 Live Demo and Obtain a 3-months Non-binding Trial
Effective and easy-to-use IT security management system based on the latest standards and regulations — from planning and establishing the security concept to certification.