Advanced Customization and New Standards: ISO 27019 & US Cybersecurity Maturity Model
Recent global challenges and digitalization enforce organizations to strengthen their security more than ever before. All of these factors together make compliance one of the hot topics today. Infopulse SCM is always keeping pace with the tendencies, partner expectations, and the tender demand continuously adding new features to boost the functionality and user experience with the solution.
Exceptional Customization: Any Standard – Any Process
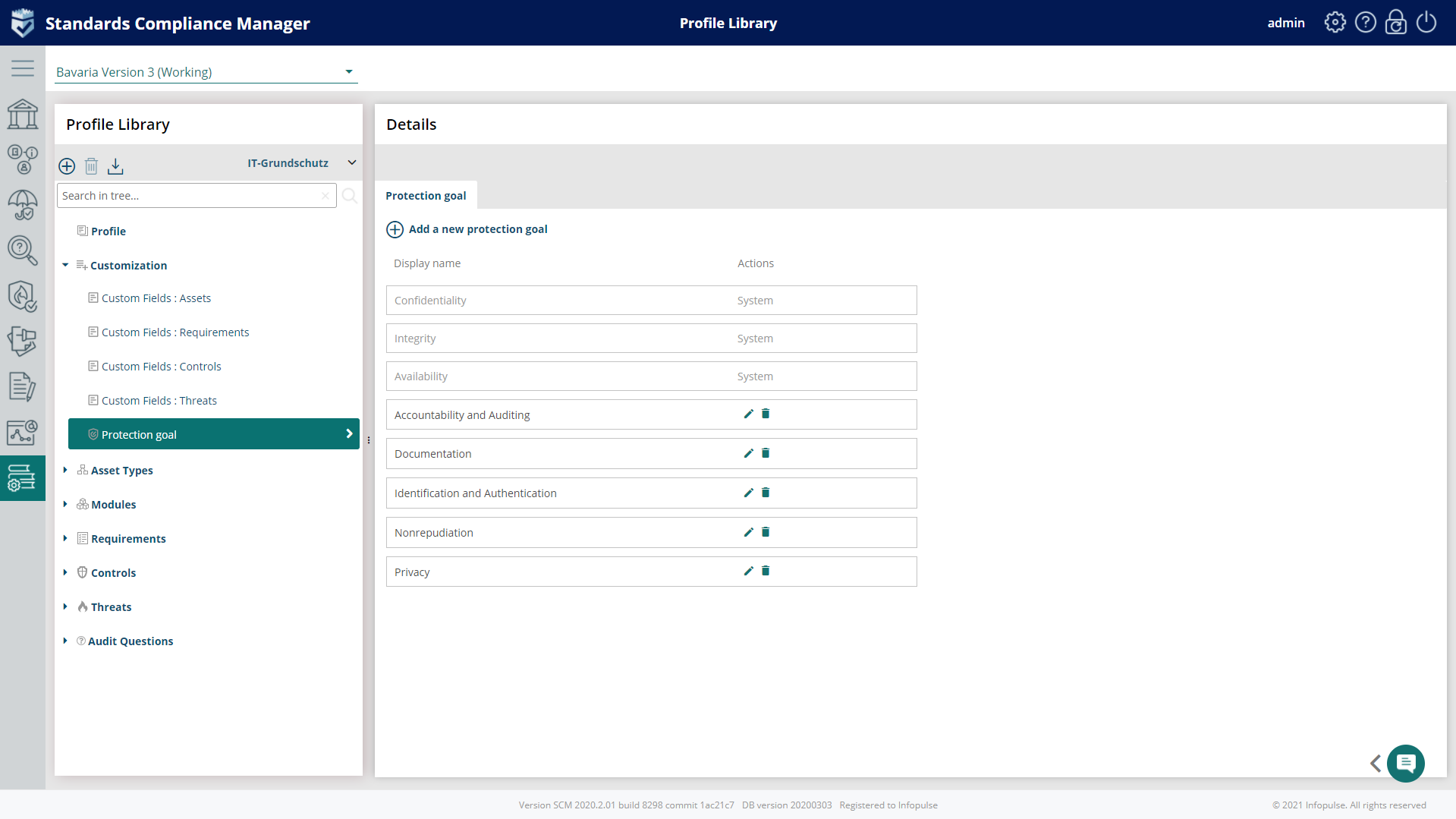
User-defined Protection Goals
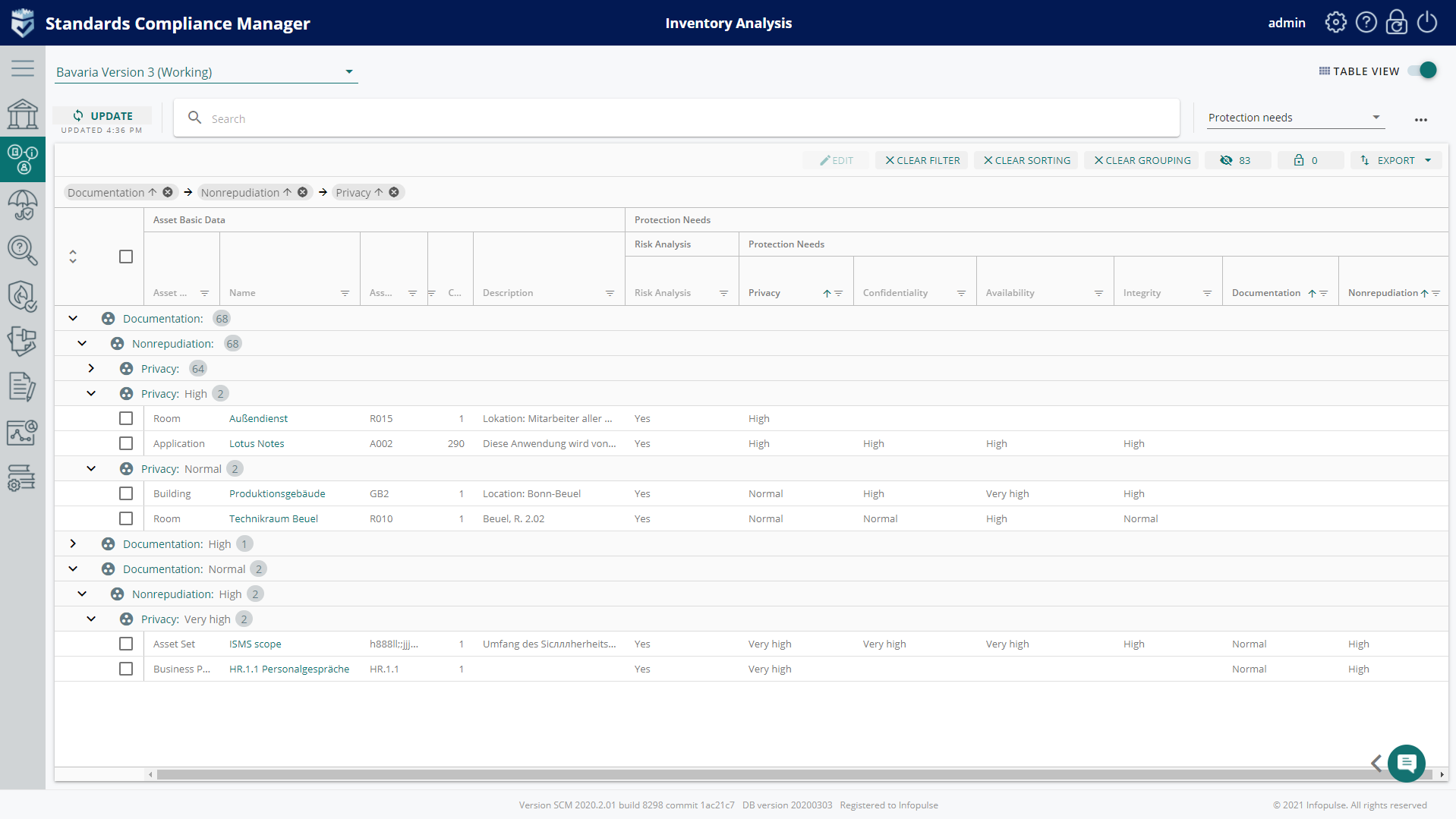
In Infopulse SCM, three core principles of information security – Confidentiality, Integrity, and Availability were previously set by default (according to IT-Grundschutz). Current SCM version allows users to create custom protection goals (i.e. Unlinkability, Transparency, Intervenability) in the Profile Library in the context of every concept version depending on the Standard requirements.
The new functionality will allow you to:
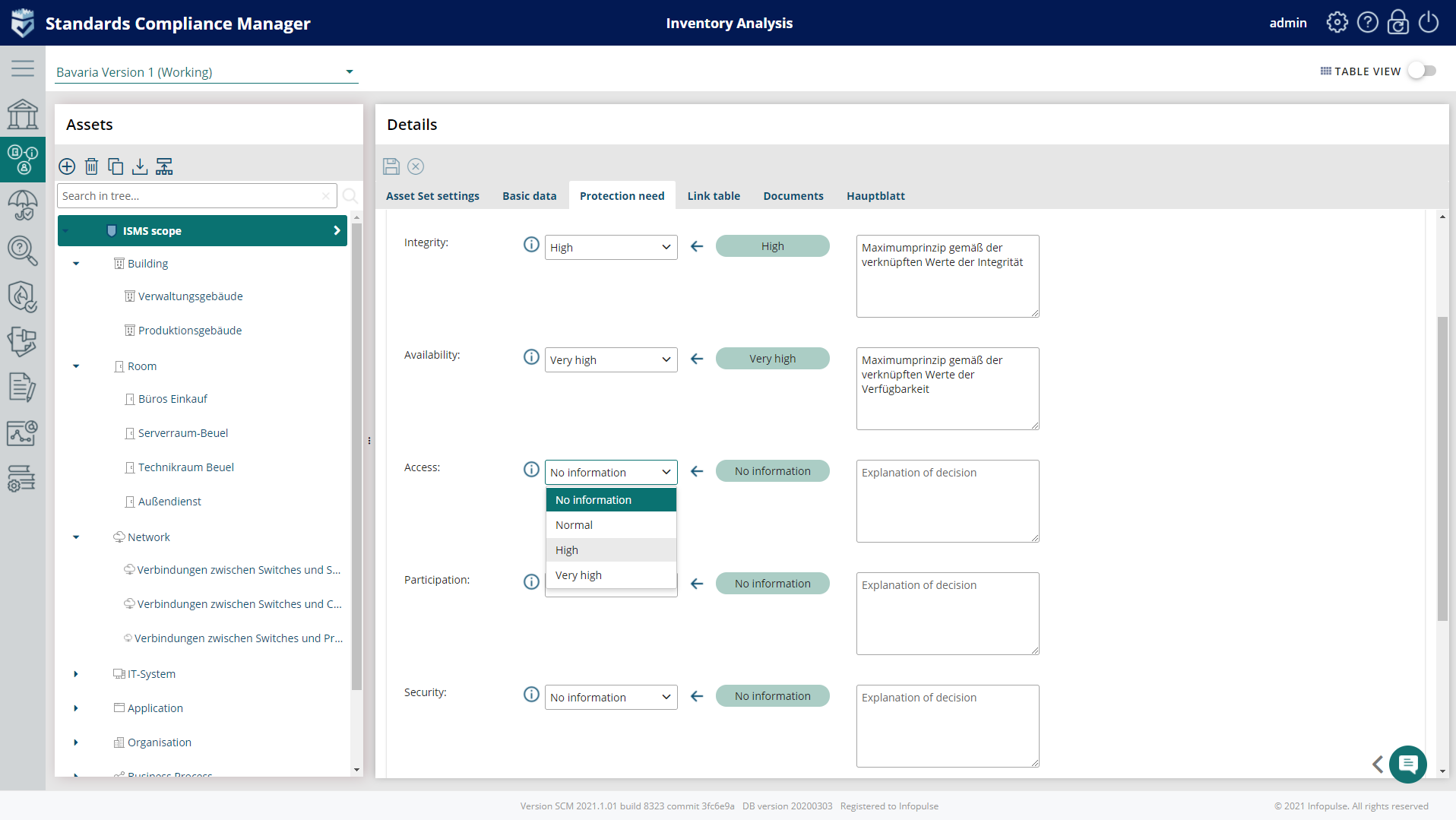
- Define new Protection requirements for assets;
- Create Protection goals using custom fields in Profile Library;
- Set inheritance of Protection requirements based on the maximum principle of their subordinate Assets linked directly – manually or automatically;
- Set inheritance for custom Protection Needs; the principles can be applied manually or automatically;
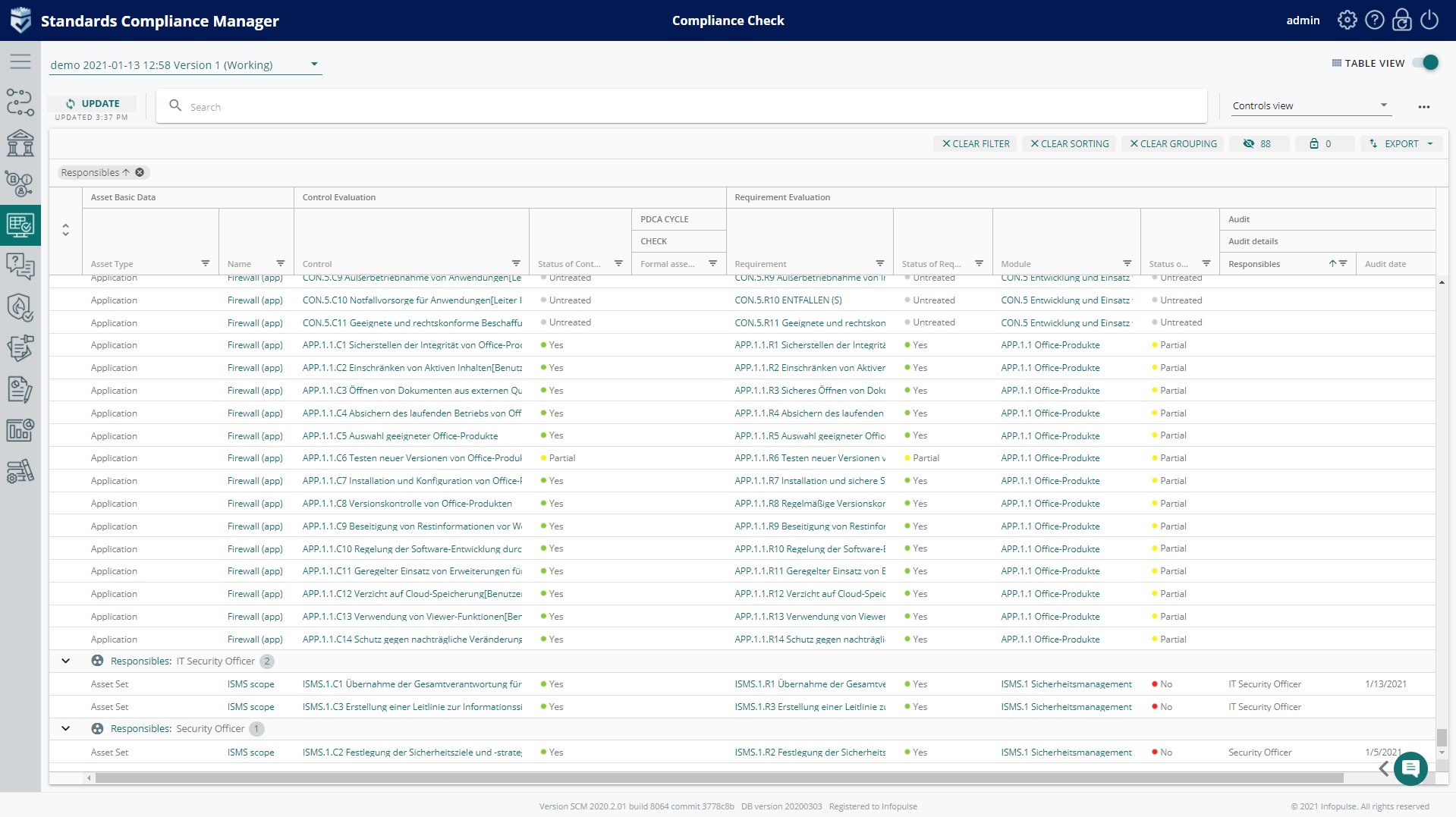
- Work with custom protection requirements in grids: Inventory Analysis, Compliance Check, and Risk Analysis grids;
- Generate reports with Custom Protection requirements: A.2 Protection Requirements report, Suggestions on Risk category standard reports in A.5 Risk Analysis.
Benefits:
- Customization of compliance and risk modeling to fit your workflow and your specific protection goals;
- Ability to follow the requirements of any standard (e.g. SDM requires 7 protection requirements);
- High accuracy of ISMS due to the extended number of protection requirements.
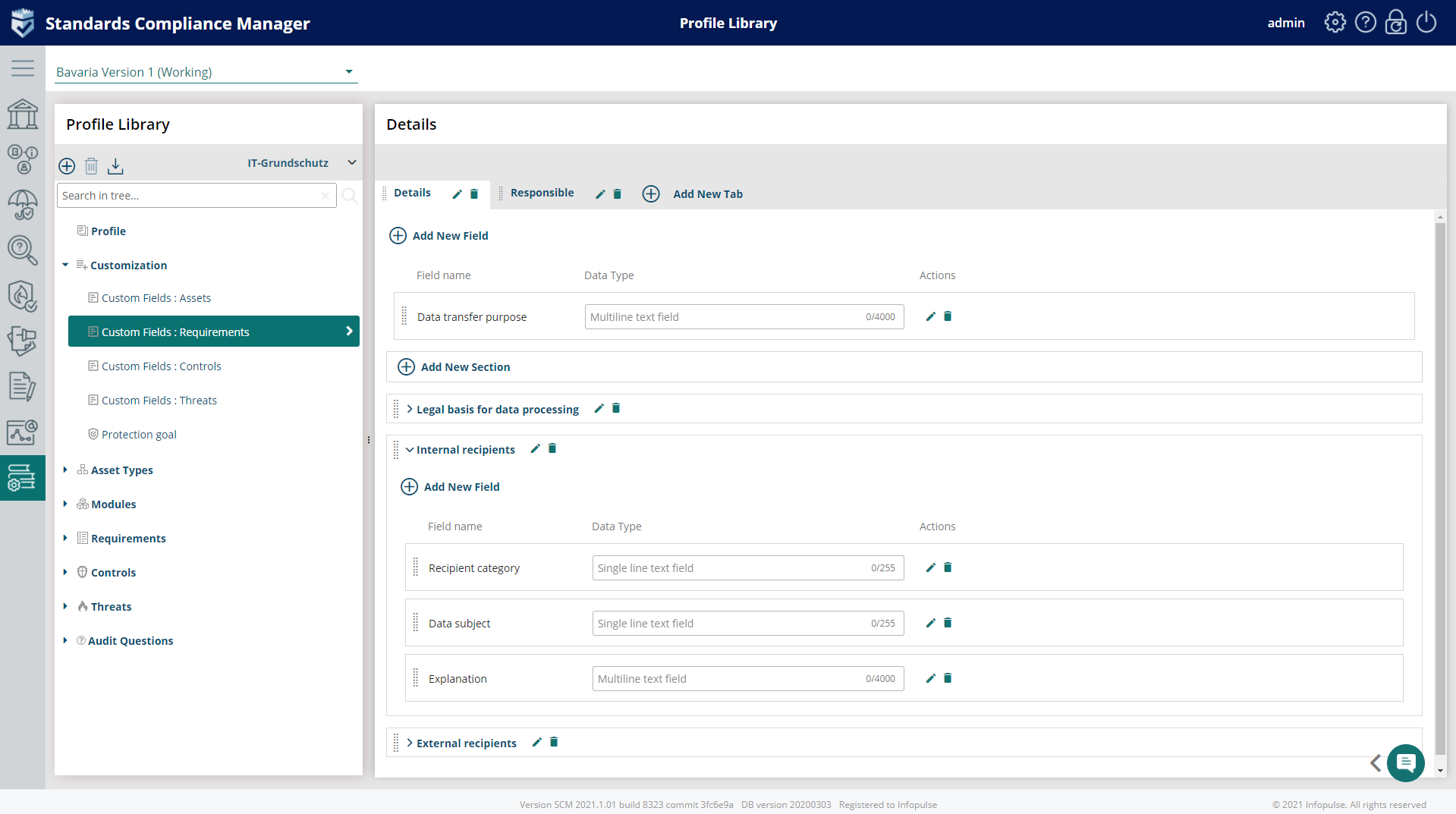
Custom Fields for Entire SCM
Customization possibilities for Compliance Check and Risk Analysis modules are dramatically improved via custom fields’ functionality. From now on, the user will be able to add custom fields to requirements and controls. Custom fields available system-wide enable users to reach the flexibility of setting up data flows, adding necessary information, and analyzing it in a smart grid.
Import of Requirements, Controls, and Threat catalogs
The new version of Infopulse SCM enables users to flexibly import Requirements/Controls or/and Threats to selected concepts available in Profile Library Tab.
Benefits:
- Enhanced customization & higher flexibility;
- Individualization of controls’ specifications and linking them to match your company’s needs;
- Freedom in choosing any control to any requirement;
- Improved operational usability and time-saving.
Efficiency and Transparency of the Organization Management
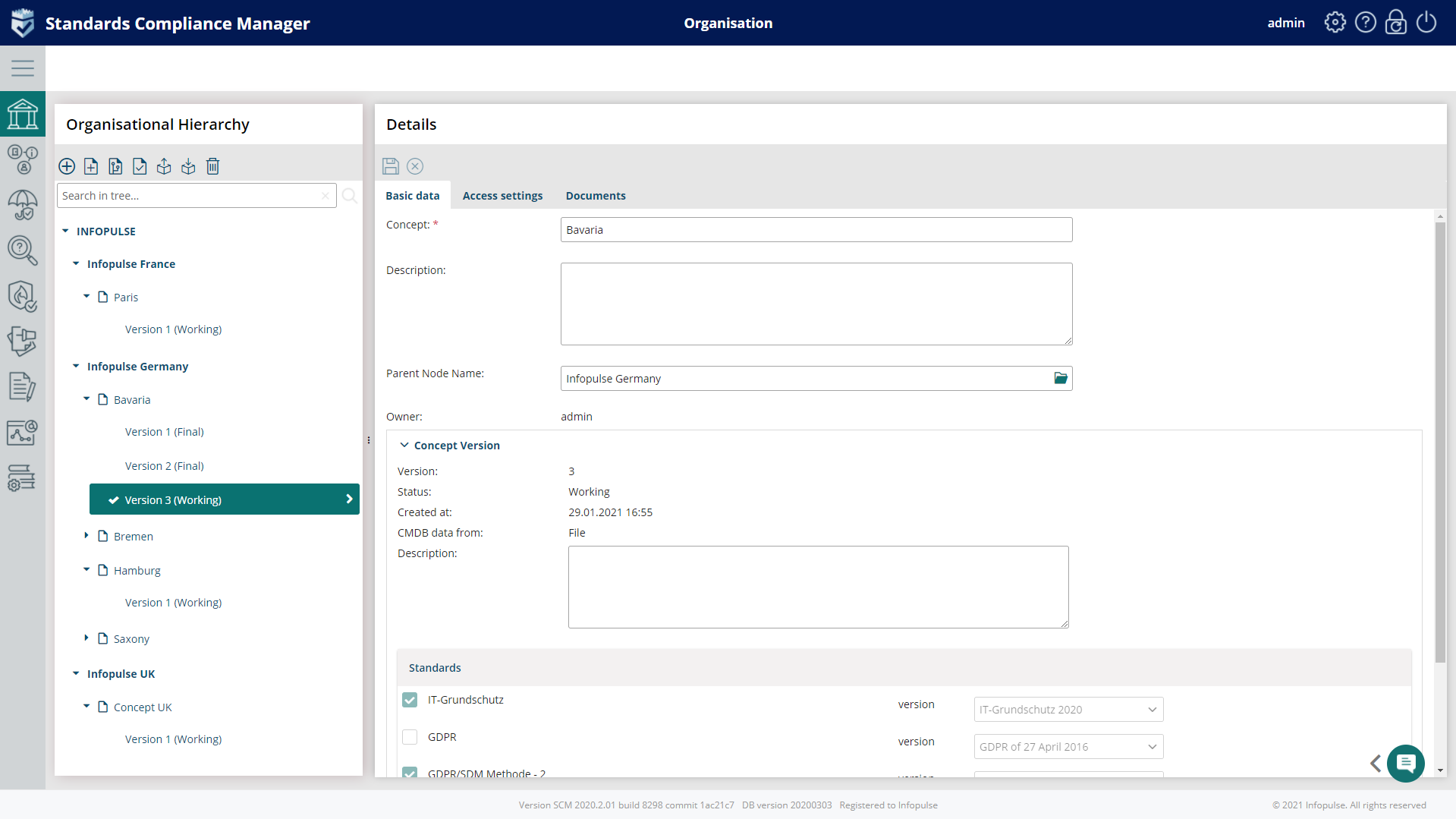
In the new release, we have adjusted SCM to the enterprise level by adding a possibility to support multi-tenancy and hierarchical organizational structure. The Concept Management module has been extended with new features and renamed to Organization Management.
In the Organization tab, users can build company structure and organize compliance concepts and projects according to the specifics of their organization. Each level in the hierarchy contains all necessary information, such as basic data (Name, Descriptions, Owner, etc).
The new permission model fully supports the hierarchical structure, as it is possible to grant/restrict distributed access to all levels of organization structure and concepts.
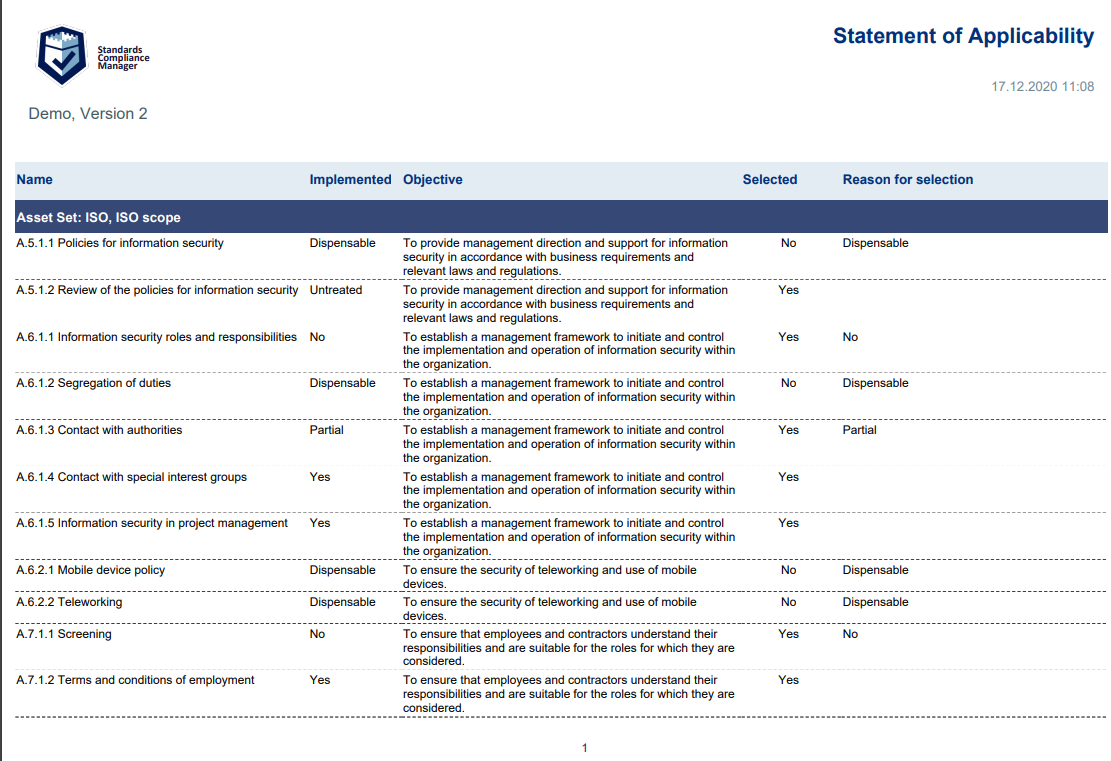
Enhanced Reporting
Based on customer feedback, we have optimized and improved our Reporting function by adding one-click generation of SoA (Statement of Applicability) reports. It is one of the key documents you must complete according to ISO 27001. The report identifies the selected controls to address information security risks, explains why those controls have been selected, states whether they’ve been implemented, and explains why any Annex A controls have been omitted.
The Rise of Multistandard Management
Today’s economic, regulatory, and tech trends require companies to become more flexible and make their compliance strategies all-encompassing and centralized. In its turn, Infopulse SCM allows organizations to support such a holistic approach to compliance due to the modular structure.
In this release, we broaden the horizon by adding two new standards: ISO/IEC 27019:2017 and US Cybersecurity Maturity Model.
ISO 27019: Security for Energy Industry
From now on Infopulse SCM supports an energy industry-specific standard ISO 27019. Based on ISO/IEC 27002, it is a set of information security controls for the energy utility sector. It covers security assessment, risk management, performance control, and monitoring all in one place.
Whether you have already used ISO 27001 in your organization, or are in the early stage of implementation, you will be able to quickly and easily adjust your existing ISMS to ISO 27019:
- Add and review controls and requirements of the standard in the compliance check;
- Work with industry-specific requirements, threat catalogs, and controls and improve them;
- Use visual distinctions of the new controls with the tag “Energy” for quick and easy navigation.
US Cybersecurity Maturity Model
Infopulse SCM expands the range of standards with the Cybersecurity Maturity Model Certification. CMMC is a unifying standard that the US Department of Defense applies to Defense Industrial Base (DIB) contractors to ensure they properly protect sensitive information.
This certification model is a collection of best practices aiming to standardize cybersecurity preparedness. The CMMC has five security levels, ranging from basic cyber hygiene to progressive security operations, presenting the degree of adherence of maturity adoption by a company. Prior to every level of certification organizations need to improve their processes according to the model’s requirements.
We are holding a webinar on the practical implementation of Infopulse SCM release 8.2 – on March, 11, 2021 at 2 pm CET. Reserve your free spot now to see how easily any process of any standard can be customized with the new functionality.
Try Compliance Aspekte For Free
Book a 1-2-1 Live Demo and Obtain a 3-months Non-binding Trial
Effective and easy-to-use IT security management system based on the latest standards and regulations — from planning and establishing the security concept to certification.