Companies that Trust Us
Benefits of ISO 27001 Certification

- Establish an information security management system and eliminate gaps in IT security
- Win more clients and secure your current customers
- Meet requirements of public and corporate tenders
- Avoid data breaches, huge fines and reputational damage
- Heighten information securing awareness among your employees
Why implement ISO 27001 with Compliance Aspekte?
Mit Experten sprechen- Easy coordination and optimization of the diversity and complexity of assets in line with your objectives and priorities
- Holistic view across ISO 27001 compliance program
- Access to regulations knowledge database and risk management recommendations
- Regular updates of the regulations available with each new SCM release
- Extensive risk management system: adaptable catalog of threats specific to an individual organization
- Prioritized risk recognition to protect critical assets
- Identification of threats and vulnerabilities
- Ability to implement information security and data protection systems with a single tool
- Implement multiple information security and data protection standards using an integrated compliance tool
- Reuse corporate catalogues of conrols
Testimonials
We were new to compliance and ISO 27001 implementation and had to go through the sophisticated certification process. Puzzled by the regulatory complexity, we wanted to find the best way for us to get started. Our project manager (aka security officer) had never worked with such compliance aspects and rules before. So we decided to get third-party assistance and signed up with Compliance Aspekte. Their guided approach has played a vital role for us. They had all the detailed explanations for compliance checks and risk analyses, including suggestions on how to handle it practically.
Compliance Aspekte is very user-friendly and customization is easy. We can conduct ISO compliance, and data protection…we can make anything we want in one tool. And this is the only tool with which it is possible. It helps us to keep the data consistent and simplify audits. The Compliance Aspekte tool is better than the existing competitors on the market and at the same time cheaper.
Constantly evolving regulations such as BSI IT-Grundschutz and GDPR are a must for us as a healthcare organization. As critical infrastructure providers, we need reliable and customizable compliance software. It was easy to adapt Compliance Aspekte to our processes. We can assess our clinic’s areas and processes in terms of security and data privacy. Besides, it enabled us to maintain a complete compliance record for the BSI IT-Grundschutz and GDPR (DSGVO) audit.
Free 3-month trial
Book it now

Useful features of Compliance Aspekte for ISO 27001 implementation
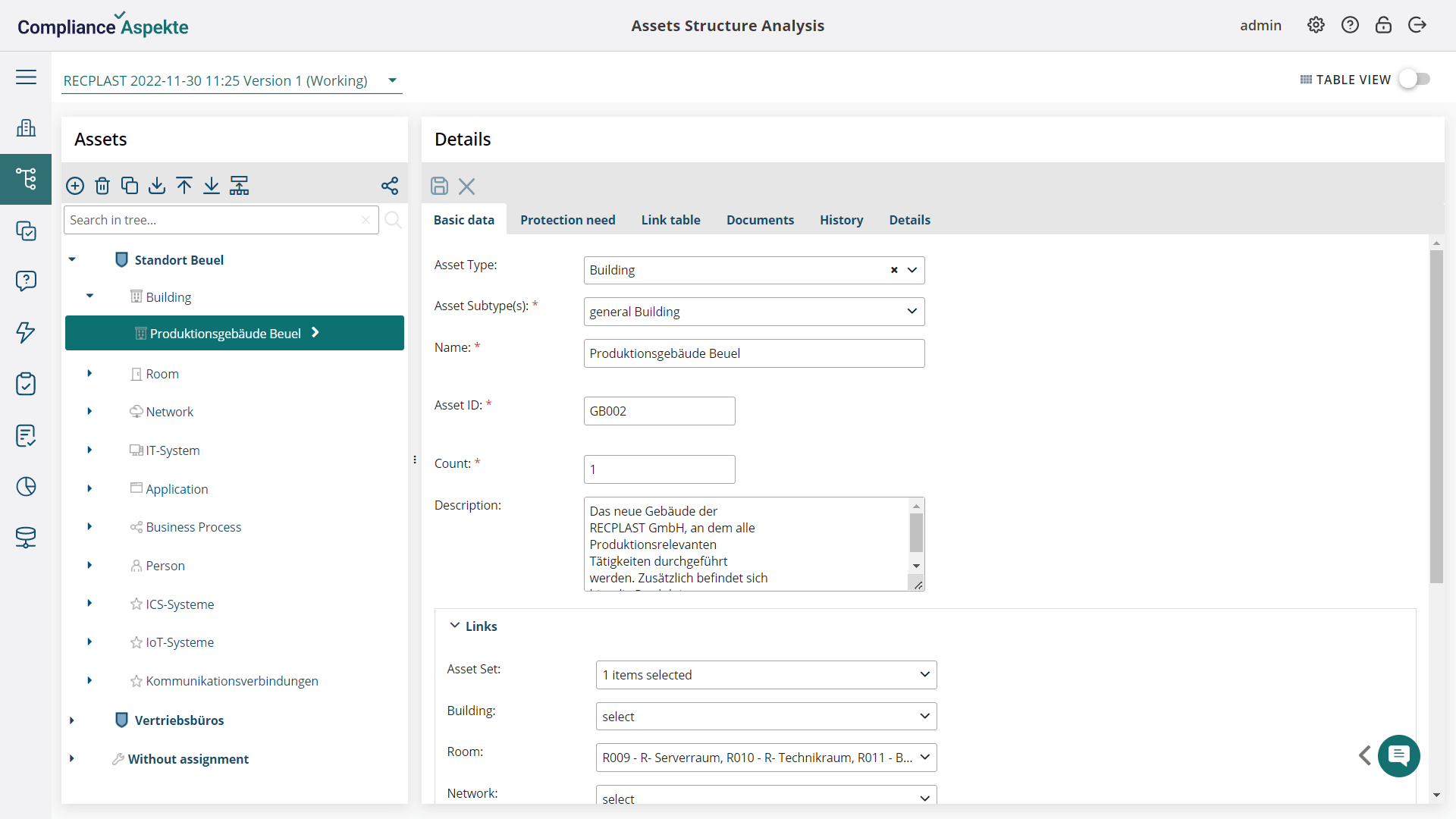
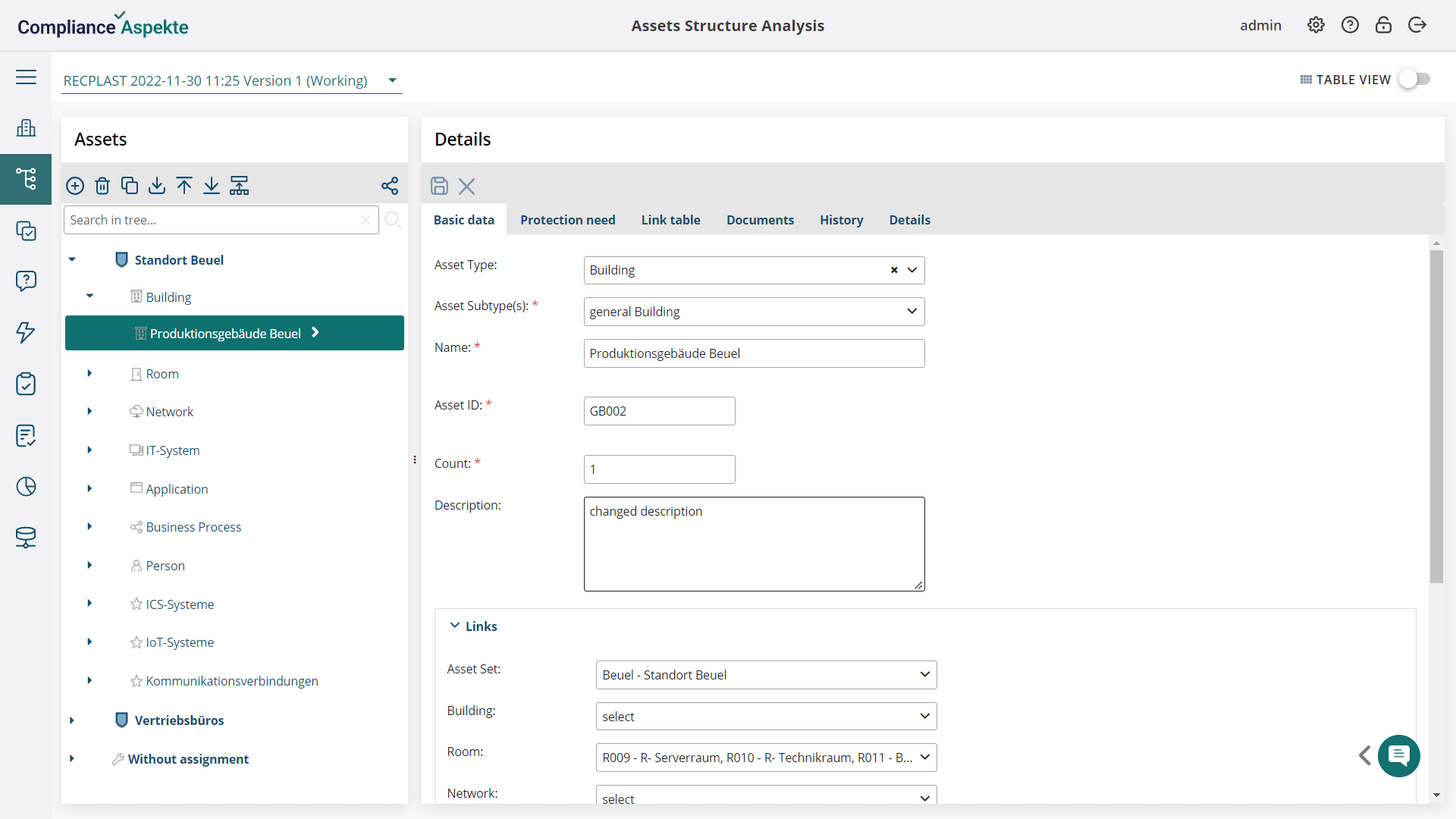
Talk to our expertsInventory Analysis
Compliance check & Risk Management
Compliance assessment according to security and privacy requirements (ISO 27701)
Automatic mapping of controls to requirements and assets (Сatalog of controls from ISO 27002)
Task management and alerts
Performance monitoring through Dashboards
User-defined Reporting
Integration with CMDB and other systems
Import and export of data from/to external systems
Sharing access to particular assets via a link and enabling easy team collaboration
Helga-bot helping on each stage of the BSI ISO 27001 compliance journey
Enjoy seamless data migration with import/export to Excel files
How to get started with Compliance Aspekte
You are a compliance expert or have a compliance expert in your team
You would need the assistance of our compliance consultants
Try for free
FAQ

The ISO 27001 standard outlines requirements for ISMS ISO 2700. The ISO 27000 family is centered around ISO 27001, which is one of the most essential standards.
The ISO 27001:2013 standard sets out the framework for an Information Security Management System (ISMS). It is essential to obtain ISO 27001 certification in order to safeguard the most valuable assets of any organization.
Any organization that wishes or is required to strengthen its business processes in the area of security, privacy, and information asset protection should apply for ISO 27001.
The size and revenue of a company do not dictate the need for ISO 27001 compliance of an organization. Even the smallest of companies may have customers or stakeholders, who need to be assured of their partners’ security.
Obwohl es sich um eine der beliebtesten und begehrtesten Sicherheitszertifizierungen auf dem Markt handelt, bleibt ISO/IEC 27001 wünschenswert, aber nicht verpflichtend.
The overall ISO 27001 cost consists of the expenses for preparing for assessment, implementing compliant security systems, security workshops, training and tests for the team, and internal and surveillance audits in 2 and 3 years. Thus the final ISO 27001 price depends on a lot of factors, including company size, the current state of information security, the complexity of ISMS, and others. At the end of the day, 27001 certifications may cost both €5,000 and €35,000. Using a practical compliance tool like Compliance Aspekte streamlines the ISO 27001 preparation, ensures data integrity, and thus significantly cuts costs.
Same as with the cost, a lot of factors have an impact on the ISO 27001 implementation length. Present information security performance, size of the organization, information security expertise, business maturity, and team involvement affect the certification process. Overall the ISO 27001 certification can take from 3 to 15 months.

Effective and easy-to-use IT security management system based on the latest standards and regulations — from planning and establishing the security concept to certification.